Download the audio
Slide 1. Introduction.
The class develops how a vehicle can be hacked, the measures that can be taken to reduce the risk, and the implications for fleet management.
Slide 2. The 5 ways to hack a vehicle.
- Vehicle Hacking.
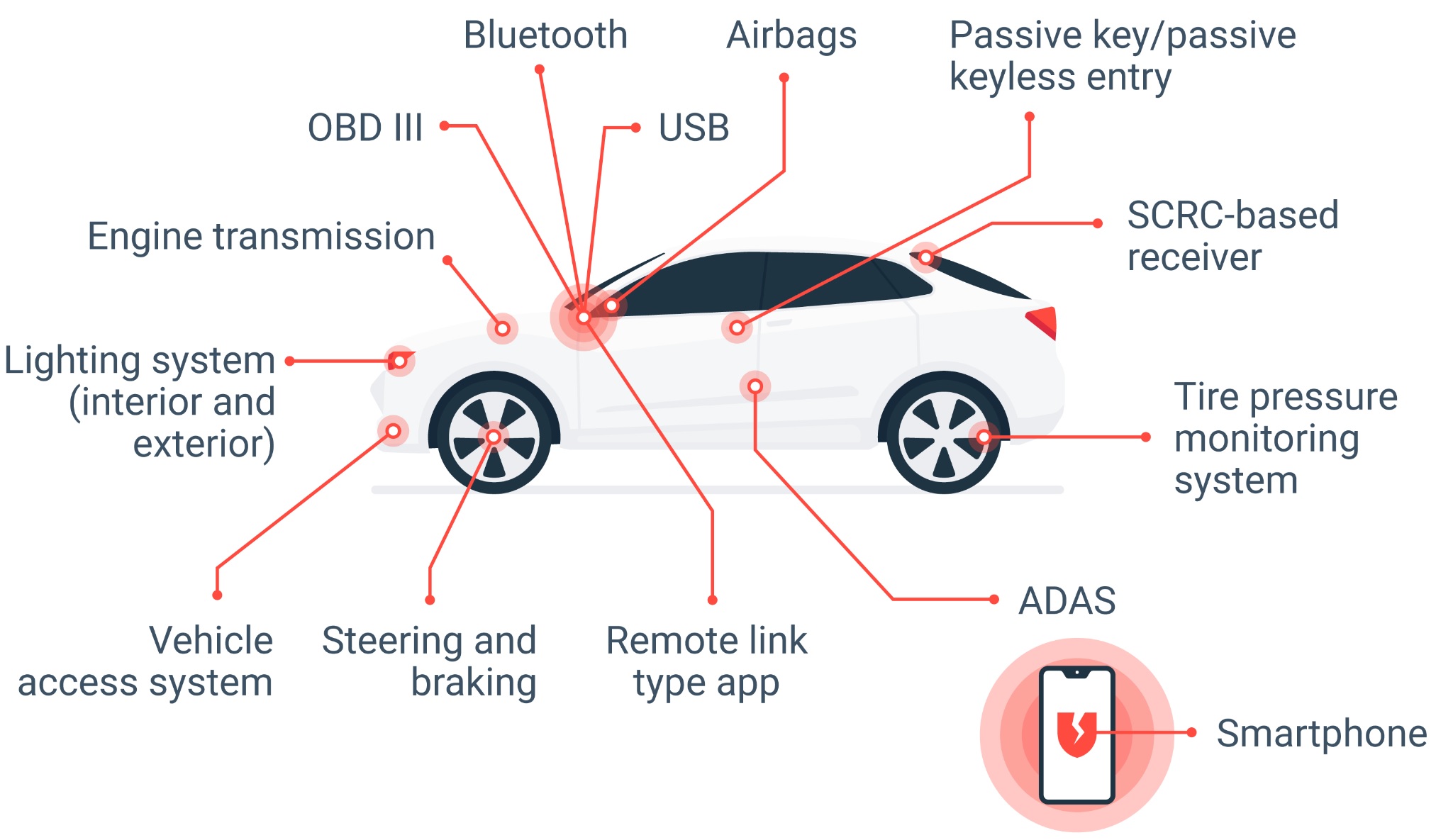
Modern cars are becoming increasingly secure from a mechanical standpoint, but they also rely more heavily on electronic systems, software, and connectivity. This evolution has not only opened the door to new possibilities but also to new vulnerabilities.
Today, stealing a vehicle does not always require breaking a window or picking the lock. In some cases, it is enough to exploit technological flaws or manipulate the electronic systems to open, start, or disable it.
Manufacturers have been strengthening vehicle cybersecurity for years, and since 2024, European regulations have required specific measures to protect them. Even so, there are several known ways in which thieves can manipulate or “hack” a car.
- The consequences of a hack.
- Loss of physical control.
Attackers can take control of critical systems such as the accelerator, brakes, or steering, which can lead to serious accidents.
-
- Vehicle theft.
Hackers can disable security systems and unlock the electronic locks to steal the car.
-
- Ransomware and system lockout.
Attackers can lock the infotainment system or completely immobilize the car, demanding a ransom to unlock it.
-
- Privacy violation.
Access to personal data stored in the car’s system, such as frequent routes, phone contacts, call logs, and real-time location.
-
- Manipulation of functions.
Malicious activation of functions such as lights, windows, windshield wipers, or the horn to distract or intimidate the driver.
-
- Spread of malware.
If an infected car connects to a diagnostic machine at a repair shop, the malware could infect other vehicles.
- The most common ways to hack a car.
Car thefts and immobilizations using technological tools can be carried out in various ways, depending on the car’s system and the method used by the criminals. Not all of these methods involve computer “hacking” in the strict sense: some require physical access to the vehicle, while others exploit wireless signals or specific functions of the car’s systems.
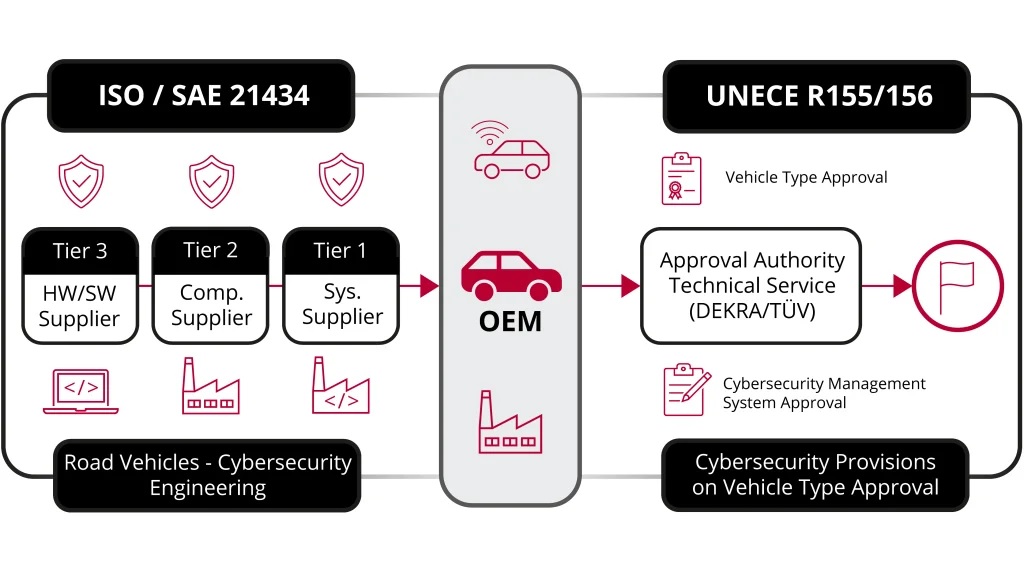
Starting in July 2024, all new vehicles sold in the European Union must comply with the new cybersecurity requirements established by the international regulations UNECE R155 and R156. These standards require manufacturers to identify vulnerabilities, protect the vehicle’s electronic systems, and ensure secure software updates throughout the vehicle’s lifespan.
The goal is to reduce the risk of cyberattacks and improve the security of connected cars, which increasingly rely on electronic systems and digital communication.
1. Through the OBD-II port.
The OBD-II port is a standard connector found in all modern cars. It is used to diagnose malfunctions, check engine parameters, and program certain vehicle functions.
The problem is that if someone gains physical access to the interior of the car, they can use that same port to reprogram a new electronic key or modify the ignition system.
This method usually requires the thief to have already broken into the vehicle, but once inside, it can allow them to generate a valid key in just a few minutes using specialized tools. For this reason, some manufacturers have begun incorporating electronic locks or additional safeguards to restrict access to critical system functions.

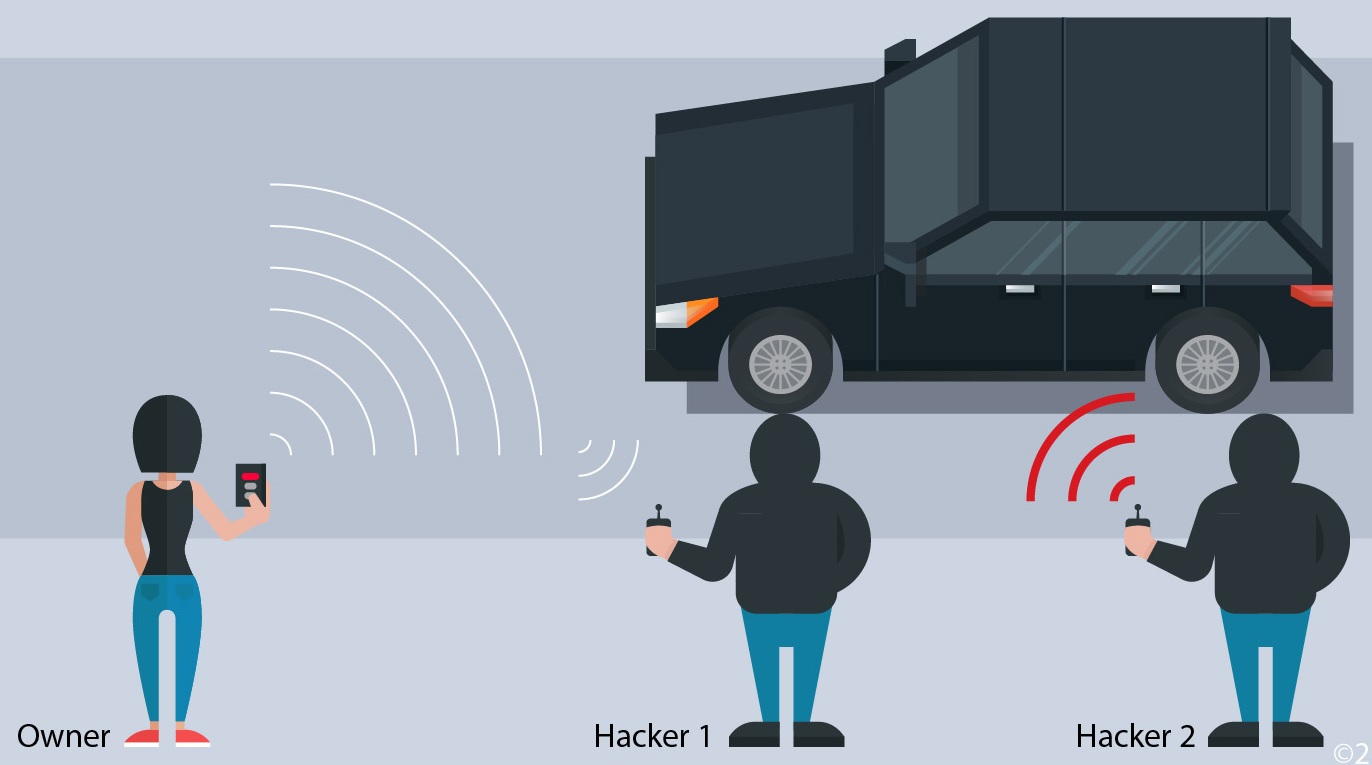
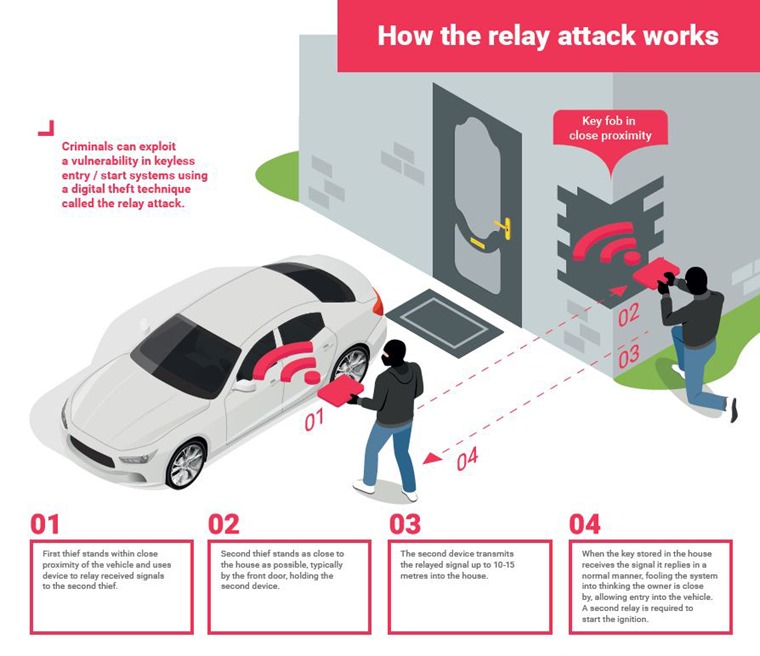
2. Signal amplification theft using keyless systems.
Many modern vehicles use keyless entry systems. These systems allow you to unlock and start the car simply by carrying the electronic key in your pocket. The downside is that criminals can exploit this technology through a signal amplification attack. In this type of theft:
Ø A device captures the key’s signal inside the parking lot.
Ø Another device amplifies that signal near the car.
Ø The vehicle believes the key is present and unlocks.
This method does not require breaking into the car or cloning the key; it simply tricks the system into thinking the key is nearby. Various studies have shown that many vehicles with keyless entry may be vulnerable to this type of attack if they lack additional safeguards.
3. Tampering with connected systems or vehicle ports.
Some vehicles allow external devices to be connected via USB ports or other connection systems to play music, update software, or interact with the multimedia system. In certain cases, these ports can become a potential entry point if tampered devices or malicious software are used.
Although this type of attack is less common than other methods, automotive cybersecurity experts point out that any system connected to the vehicle’s software can become a gateway if it is not properly protected.

4. Accessing the vehicle’s electronic network.
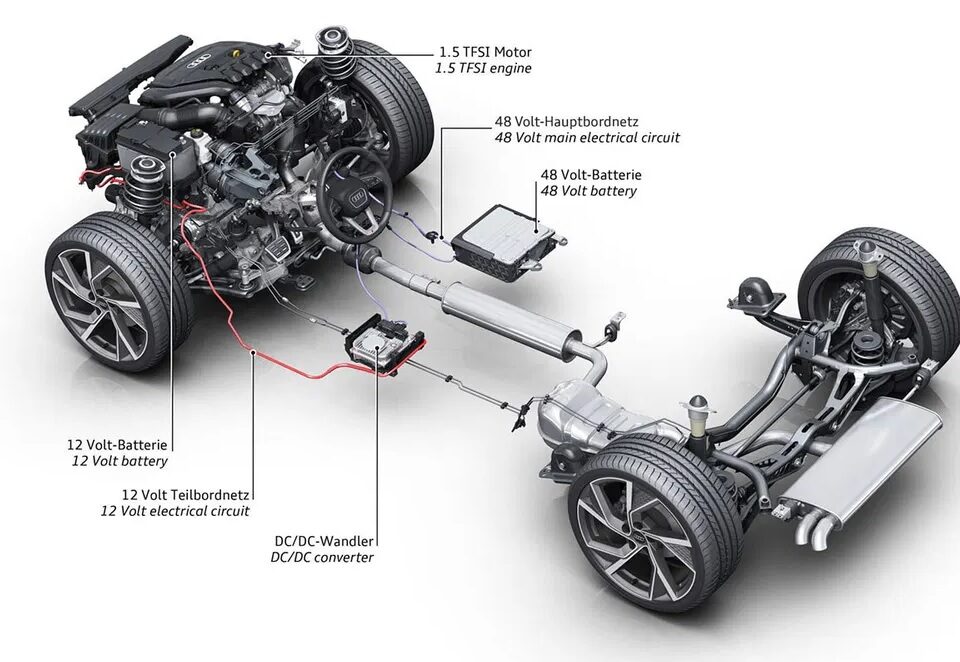
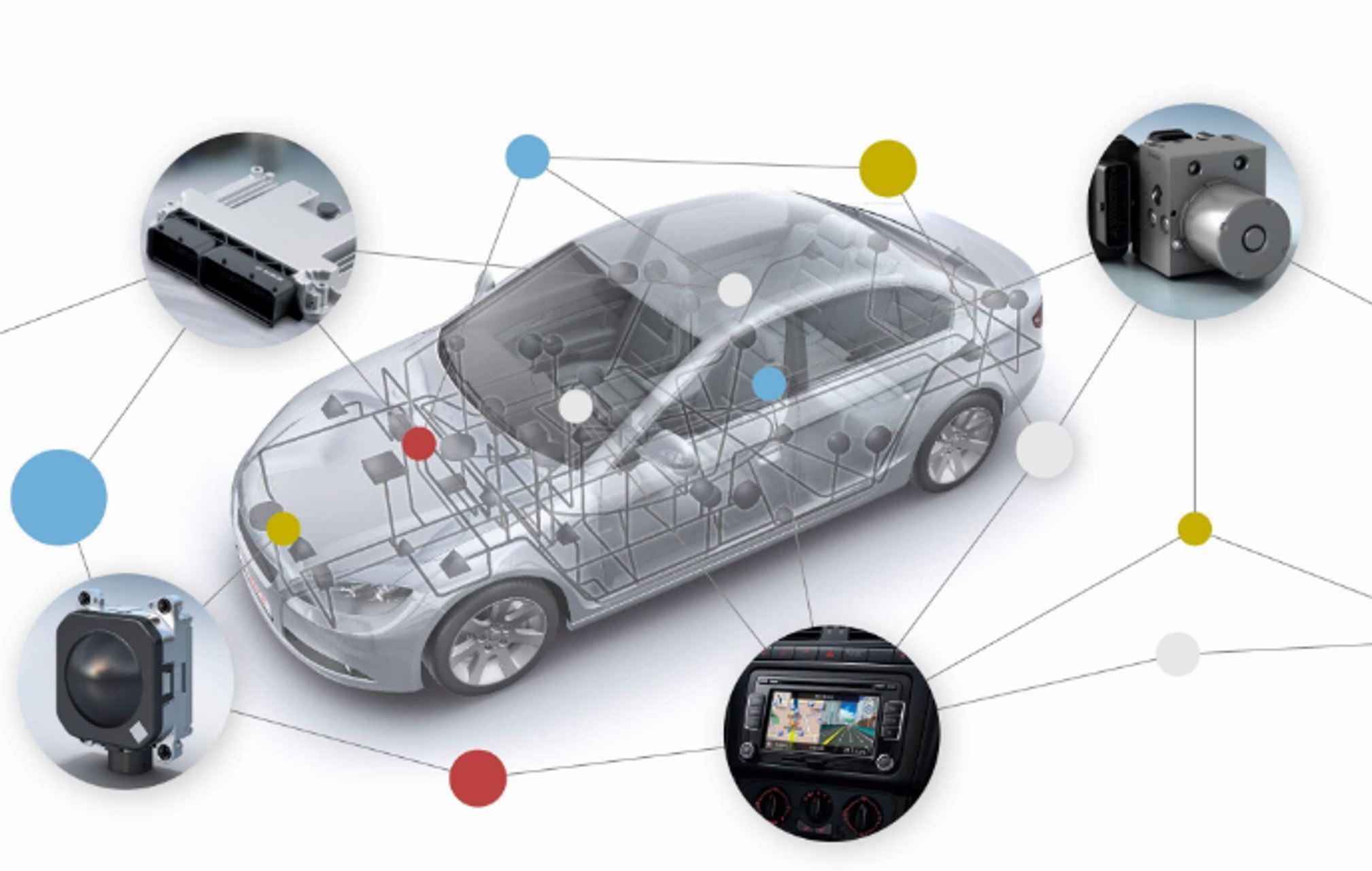
Modern cars function as veritable computer networks on wheels. Various electronic control units manage systems such as the engine, brakes, steering, driver assistance, and safety systems, and communicate with one another via internal networks, such as the CAN bus (Controller Area Network).
If an attacker manages to gain access to this network, typically through physical access to the car or via connected devices, they could manipulate certain vehicle functions. This is a complex type of attack that is rare in everyday thefts, but it is part of the scenarios studied by automotive cybersecurity specialists.
5. Through the car’s connected apps or services.
Many modern cars come with mobile apps that allow users to unlock the vehicle, check its location, or control various functions remotely. These apps require user credentials, so unauthorized access could allow third parties to interact with the vehicle.
Risks can arise, for example, if:
Ø Weak passwords are used.
Ø Credentials are shared.
Ø The mobile device is compromised by malware.
Ø The app or the car’s software is not up to date.
For this reason, manufacturers recommend using strong passwords, additional authentication, and always keeping the vehicle’s software up to date.

- What to do if your vehicle is stolen.
If your car has been stolen, it’s important to act quickly to help locate it and complete the necessary insurance paperwork. Here are the main recommendations:
1. First, check to see if the vehicle has been towed by the city tow truck. Sometimes a car may have been towed because it was parked illegally or for road safety reasons.
2. Report the theft to the police as soon as possible. The sooner the report is filed, the sooner search procedures can be initiated.
3. Provide all vehicle details: license plate number, make, model, color, and any distinctive features that may help identify it.
4. Contact your insurance company to report the theft and initiate the appropriate procedure based on your policy coverage.
5. If the vehicle has a tracking system or connected app, provide that information to the authorities to facilitate its recovery.
Acting quickly can increase the chances of recovering the vehicle and streamline subsequent administrative procedures.
- Theft of fleet vehicles.
The most commonly stolen vehicles are passenger cars, vans, and SUVs, because they are in high demand and are often sold in other countries or used for parts.
Trucks and specialized vehicles are rarely stolen because demand for them is very low.
Fleet vehicles bearing the logos of our company, government agencies, etc., are rarely stolen because they are easy to track, and the thieves would have to remove all the branding to sell them.
Most fleet vehicles have their own parking facilities and are not usually parked on the street at night, so they are at lower risk of theft.
In general, fleet vehicles have a low probability of being stolen, although this can happen with unmarked passenger cars, vans, and SUVs.
Vehicles transporting valuables or money are at the highest risk of being targeted, because what matters most to thieves is not the vehicle itself but what it is carrying.
Vehicles transporting money, high-tech items such as computers, tablets, and smartphones, and works of art are the fleet vehicles most likely to be targeted for theft.
- Implications for fleet management.
The main consequence of a cyberattack on a fleet is that the vehicles are locked, rendering them unusable, and the attackers demand a ransom in cryptocurrency to unlock them.
Another consequence is that the vehicle itself, or the cargo it is carrying, may be stolen.
We recommend taking the following measures.
- Hire an external consulting firm.
Even if the vehicle complies with UNECE Regulations R155 and R156, vehicles today still have vulnerabilities. There are consulting firms specializing in vehicle cybersecurity that can advise you on the measures to take to prevent your fleet vehicles from being hacked.
These consultants specialize in vehicle cybersecurity, and as fleet managers, we do not possess the same level of knowledge or experience they do.
Keep in mind that cybersecurity technology and new methods of vehicle hacking evolve rapidly, and these consultants stay up to date.
- Establish a protocol and security measures.
You must establish a protocol that specifies which security systems and measures the vehicles must have, that drivers cannot install apps or use the USB port, how often new software updates must be installed, etc.
- Driver and user training.
Drivers must be trained on what they can and cannot do with the vehicle, such as installing unauthorized apps or connecting their phone to the vehicle via USB or Bluetooth.
- Vehicle procurement.
Purchase vehicles that comply with UNECE Regulations R155 and R156, although they still have vulnerabilities.
- Use telematics.
Telematics allows you to track the location of vehicles in the event of theft, and can also alert you in real time if goods are being stolen from a truck or van.
- How to Reduce the Risk of Car Theft.
Although no system is completely foolproof, there are some simple steps you can take to help reduce the risk of theft.
Among the most common recommendations are the following:
Ø Keep your car keys away from doors or windows in the parking lot.
Ø Use covers or cases that block the key’s signal in vehicles with keyless entry systems.
Ø Always check that the car is properly locked.
Ø Avoid leaving keys or documents inside the vehicle.
- Update the software.
You should always install the latest software versions provided by the manufacturer to prevent your car from being hacked. While it’s true that vulnerabilities can sometimes be introduced through certain software updates, it’s much riskier to leave your car unupdated. In fact, most of these updates address security vulnerabilities that have been identified.
- Disconnect connections when not in use.
This is another classic security tip for electronic devices. Turning off Bluetooth or Wi-Fi when not in use is part of basic smartphone security. The same applies to a vehicle: the more doors you keep closed, the harder it will be for a hacker to gain access.
- Scan devices you plan to connect to your car.
If you’re going to connect a USB drive or other device to your car, always make sure to run an antivirus scan on it first to check for malware. These devices can provide an easy entry point for cybercriminals if they aren’t properly protected. Be careful with the vehicle’s OBD2 port if you plan to connect a device to it, for example, to read trouble codes or monitor your driving style.
- Protect your passwords.
If your car has Wi-Fi, never leave the password written down on a piece of paper in the glove compartment, and make sure it doesn’t appear on any screen when you enter it. This is especially important if you share your vehicle with others, such as if you’re part of a fleet.
- Be careful with Apps.
Smartphones and vehicles are becoming increasingly connected. For example, you can use your cell phone to lock and unlock the car, locate it when you can’t remember where you parked, turn on the heater before getting in, or even park it remotely. That is precisely why you must exercise extreme caution when downloading any app to your smartphone, as it can serve as a gateway for hackers to access all those functions.
- Selling and buying a vehicle.
If you buy a used vehicle, make sure the previous owner’s data has been deleted and all their access permissions revoked. Do the same if you’re the one selling the vehicle. It’s as simple as resetting the infotainment system to factory settings.
Slide 3. Thank you for your time.
The class has developed how a vehicle can be hacked, the measures that can be taken to reduce the risk, and the implications for fleet management, see you soon.